The cybersecurity landscape is changing with every new victim. To keep up a solid cybersecurity program in a volatile environment is incredibly challenging. This is where the Centre for Internet Security (CIS) comes into play.
The CIS provides a set of standards that helps organizations build a framework for gauging the effectiveness of their cybersecurity programs. These standards are known as CIS Critical Security Controls or CIS Controls.
What are CIS Controls?
The CIS Critical Security Controls (CIS Controls) are a recommended set of cybersecurity best practices and defensive actions that provide specific and actionable ways to thwart the most pervasive attacks and support compliance in a multiframework environment.
The CIS controls are updated through an informal community process to remain in sync with current cybersecurity best practices and an evolving threat landscape. Experts from government, industry, and academia build up this community, pooling their expertise to identify effective cybersecurity controls.
What is the purpose of CIS Controls?
The CIS Controls are important because they minimize the risk of data breaches, data leaks, IP theft, corporate espionage, privacy loss, DoS and other cyberthreats. CIS controls help companies continuously monitor and maintain cyber defenses irrespective of the alert level (low, mid or high).
The CIS Controls help address the following:
- Critical areas to establish a risk management program
- Defensive steps to provide the best value
- Track risk management program maturity
- Map your organization’s regulatory and compliance frameworks
Who uses CIS Controls?
The CIS Controls are utilized by thousands of global enterprises, large and small, and are supported by numerous security solution vendors, integrators and consultants. Some users include the Federal Reserve Bank of Richmond, the University of Massachusetts, the states of Idaho, Colorado and Arizona, and the cities of Oklahoma, Portland and San Diego.
Who has endorsed the CIS Controls?
- The CIS Controls are referenced by the U.S. Government in the National Institute of Standards and Technology (NIST) Cybersecurity Framework as a recommended implementation approach for the Framework.
- The European Telecommunications Standards Institute (ETSI) has adopted and published the CIS Controls and several of the Controls companion guides.
- In 2016, in her state’s Data Breach Report, Kamala D. Harris, then California Attorney General, said: “The set of 20 Controls constitutes a minimum level of security – a floor – that any organization that collects or maintains personal information should meet.”
- The CIS Controls are recommended by organizations as diverse as the National Governors Association (NGA) and the U.K.’s Centre for the Protection of National Infrastructure (CPNI).
- The National Highway Traffic Safety Administration (NHTSA) recommended the CIS Controls in its draft security guidance to automotive manufacturers.
What is the latest version of CIS Controls?
The latest version of V8 was launched in 2018, which was enhanced from the previous version (V7), aka the CIS Top 20. CIS Control V8 compromises the following:
- Set of 18 cyber defense Controls from the previous 20 Controls (recommendations)
- Implementation Group (IG): IGs are divided into three groups and are new recommended guidance for prioritizing the implementation of the Controls
- The new version consolidates the CIS Controls by activities rather than by who manages the devices
What’s new with the CIS Controls v8?
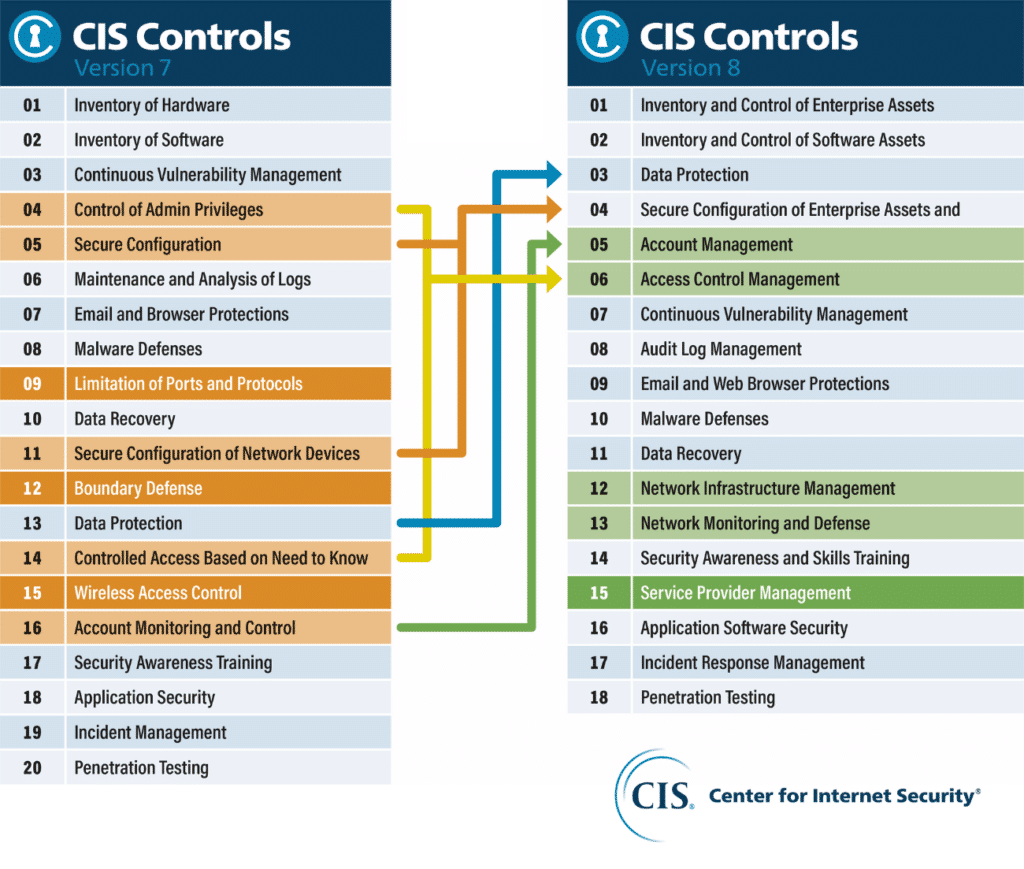
Under the latest version, the set of 18 cyber defense Controls (recommendations) is classified by activities.
Control 1: Inventory and Control of Enterprise Assets: Organizations should actively manage every end-user device connected to the infrastructure physically, virtually and remotely to their network.
Control 2: Inventory and Control of Software Assets: The active management of all software on the network, including operating systems and individual applications, so that only authorized software is installed and can be executed.
Control 3: Data Protection: Develop processes and technical controls to ensure the safety and integrity of data stored on the network.
Control 4: Secure Configuration of Enterprise Assets and Software: Ensure software (OS and applications) and end-user devices (including portable and mobile, network devices, IoT devices and servers) are configured securely.
Control 5: Account Management: Use processes and tools to assign and manage authorization to credentials for user accounts (admin accounts, service accounts, end-user devices and software).
Control 6: Access Control Management: Manage user credentials and authorization to ensure secure access control across the network.
Control 7: Continuous Vulnerability Management: Develop a plan to continuously identify and monitor vulnerabilities.
Control 8: Audit Log Management: Collect, alert, review and maintain event logs of events that could help detect, understand or recover from an attack.
Control 9: Email and Web Browser Protections: Improve protections and detections of threats from email and web vectors.
Control 10: Malware Defenses: Prevent or control the installation, spread and execution of malware by ensuring sufficient antivirus monitoring.
Control 11: Data Recovery: Establish and maintain data recovery practices to ensure successful recovery following a cyberattack.
Control 12: Network Infrastructure Management: Establish, implement and actively manage network devices to stop attackers from exploiting vulnerabilities.
Control 13: Network Monitoring and Defense: Ensure network infrastructure is monitored and maintained.
Control 14: Security Awareness and Skills Training: Establish and maintain a security awareness program to help employees identify social engineering and phishing attacks.
Control 15: Service Provider Management: Vet third-party service providers and ensure outside partners have robust cybersecurity policies.
Control 16: Application Software Security: Ensure no applications running on the network pose a security risk or create vulnerabilities.
Control 17: Incident Response Management: Establish a program to develop plans for a rapid and robust response to any security incidents.
Control 18: Penetration Testing: Run attack simulations on your network to identify weak points and fix any vulnerabilities.
CIS Implementation Groups
Implementation Groups (IGs) help organizations prioritize CIS Controls based on their resources and risk profile. There are three IGs based on the latest version.
Implementation Group 1 (IG1)
IG1 focuses on basic cyber hygiene. It is comprised of the foundational set of cyber defense Safeguards that every enterprise should apply to guard against the most common attacks. These include maintaining an inventory of all digital assets so that security teams know the totality of what needs to be monitored and protected. There are 56 foundational safeguards to help smaller companies with a smaller IT team, which includes family-run businesses, SMEs and startups.
Implementation Group 2 (IG2)
CIS Implementation Group 2 (IG2) builds upon IG1 foundational Safeguards and brings an additional 74 Safeguards to help IT teams deal with greater operational complexity. IG2 layers in additional cyber defense safeguards that prevent unauthorized software use, enable remote wipe capability for portable end-user devices, document data flows and ensure secure network authentication, to name a few. Organizations with moderate resources and greater risk exposure, like non-IT businesses and medium to large manufacturing industries, will need to implement the IG2 Controls along with IG1.
Implementation Group 3 (IG3)
CIS Implementation Group 3 (IG3) adds 23 more Safeguards directed at organizations that deal with more sophisticated forms of attack. This IG is the most complex to implement and requires cybersecurity experts that specialize in different areas. Mature organizations with significant resources and high-risk exposure from handling critical assets and data need to implement the Safeguards under the IG3 category along with IG1 and IG2.
Enhance data protection with Unitrends
Unitrends Unified BCDR is a comprehensive data backup and disaster recovery platform that supports an organization’s implementation of the CIS Controls through additional hardening and securing of the backup environment.
For instance:
- **Control 11:**Unitrends purpose-built backup appliances run a hardened Linux kernel to secure backups outside of Microsoft Window’s attack surface. Replication of encrypted backups to a secondary appliance, running at colocation or the cloud, enables disaster recovery.
- Control 9: Spanning, our cloud-to-cloud backup solution for Microsoft 365 and Google Workspace offers powerful security integrations to help protect users and accounts with automated phishing defense and Dark Web Monitoring.
- **Control 6:**Unitrends central management console, UniView, secures access to the backup environment with 2FA. Once inside the environment, Role-Based Access Control may be used to limit user access or scope within the backup environment, limiting the actions they may perform or the backups they have access to, as appropriate with the functions of their role.
Want to see how Unitrends Unified BCDR can help enhance your data protection and disaster recovery posture? Request a demo today!