The holiday season is right around the corner. Everyone is rushing to wrap up their work before the holiday break while looking forward to celebrating with family and friends. However, if you think cybercriminals are following suit and taking a break during this festive season to enjoy soaking up the sun on a beach or trekking through snow-swept woods, you are gravely mistaken. In fact, it’s the time of the year when cybercriminals are putting in extra hours, being particularly active and effective. F5 Labs reports phishing activity increases by more than 150% from October to November. Consequently, thousands of unwary individuals fall victim to holiday-related phishing attacks every year.
According to the FBI’s Internet Crime Complaint Center’s (IC3) 2021 report, non-payment or non-delivery scams cost people more than $337 million in 2021. Meanwhile, credit card fraud accounted for another $173 million in losses. The IC3 receives a large volume of these complaints in the early months of each year, suggesting a correlation with the preceding holiday season’s shopping scams.
Why are people likely to fall for holiday phishing scams
The end of the year is usually flooded with a lot of activity — holiday promotional emails, shipping notices, order receipts, charitable donation requests and more. Seasonal emails flood users’ inboxes during the festive season, creating a myriad of distractions. Cybercriminals take advantage of all these seasonal emails by spoofing them and inserting their malicious links and attachments. They deceive people into opening malware-laden files and attachments or get them to click on malicious links. All it takes is a moment when someone unintentionally lets their guard down for cybercriminals to spring into action.
As people are preoccupied with holiday shopping during this season, these scams can also come in the form of deals that seem too good to be true. They cloak their intent as legitimate businesses and trick people into engaging with them.
Smishing or SMS phishing carried out over mobile text messaging is also on the rise as consumers have started relying more on their smartphones to do online shopping. The fact that there is relatively far less security on mobile devices lends to the emerging popularity of this particular attack vector. Smishing can also occur through various non-SMS channels, including data-based mobile messaging apps.
How holiday phishing scams affect businesses
There is a general perception that phishing scams have more to do with consumers than businesses, but that’s not necessarily true in the new normal. With remote and hybrid work becoming the norm, our personal and professional lives have blurred. Employees often use the same device for work and leisure, more often check personal emails during work and festive shopping may cross the boundaries between the home and work networks. This gives attackers more opportunities to lay their hands on business-critical data.
An employee clicking on a link in a carefully crafted phishing email can risk the entire business network since the compromised device is connected to the network. Scammers can also send phishing emails to the work email purporting to be business-related. Phishing attacks thus carry a significant risk for enterprises as well.
Watch out for these holiday phishing scams
Let’s look at some of the prevalent holiday phishing scams to watch out for during this holiday season.
Fake order receipts
One of the most popular holiday phishing scams involves scammers sending fake order receipt emails that appear to be from popular retail brands like Amazon or Walmart. The goal behind such phishing emails is usually to steal money or data (see Figure 1).
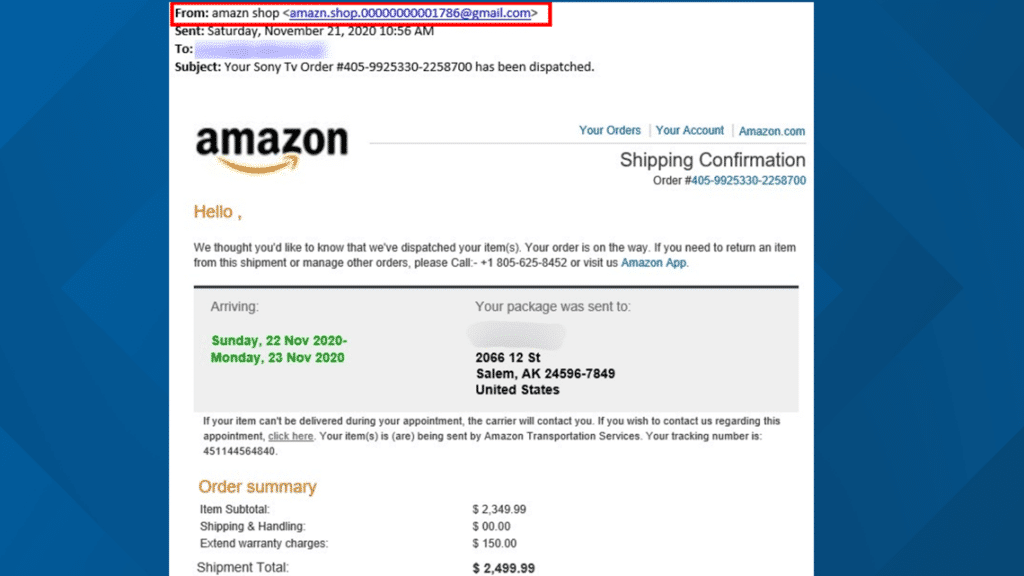
Such emails try to elicit an emotional response from people who didn’t place the order in the first place. The email would often contain links, attachments or phone numbers to lure the victims into a response. The links in the email usually direct the user to a fake sign-in form developed to steal login credentials or a malicious website.
Spoofed tracking shipments
Thanks to the surge in online shopping during the holiday season, people more often receive order tracking notifications through emails and SMS. Scammers take advantage of it and send tracking links impersonating leading logistics companies or freight carriers like FedEx or DHL.
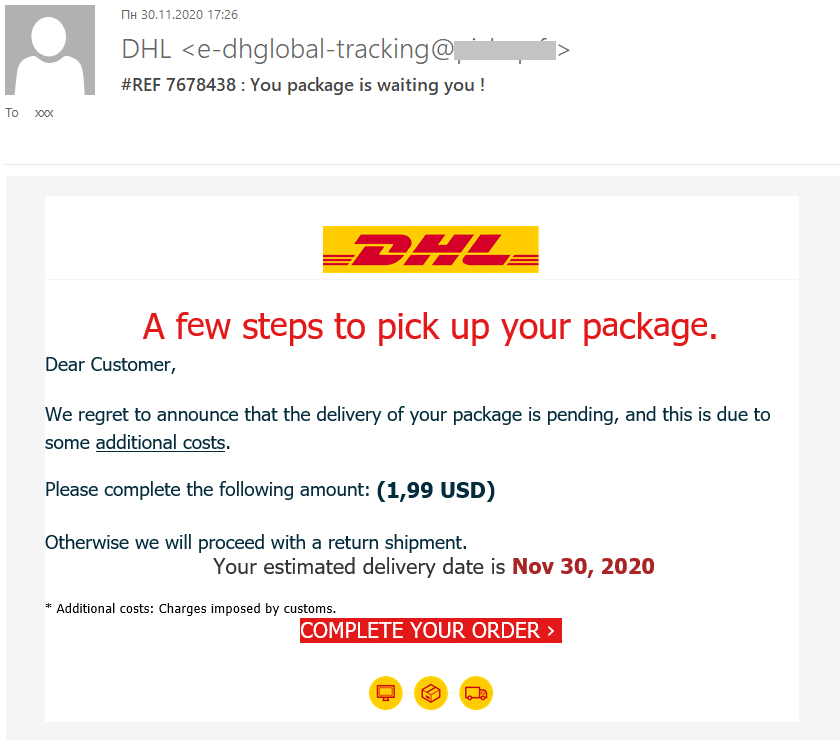
As in Figure 2, these scams trick people into believing they’re receiving a routine message from the carrier. The fake tracking links lead victims to scammers’ websites where they have to provide personal information or credit card details. What’s worse? In some cases, malware embedded in these fraudulent sites will start downloading as soon as one clicks the link.
Falsified charitable contributions
The holiday season is also the season of giving. Charities often expand their outreach efforts to raise funds during the season, and unfortunately, it also opens the door for scammers. Holiday phishing scams have recently started to exploit the giving spirit of the season, as phishers are increasingly coming up with fake donation emails and websites to steal money and credit card information from donors (see Figure 3).
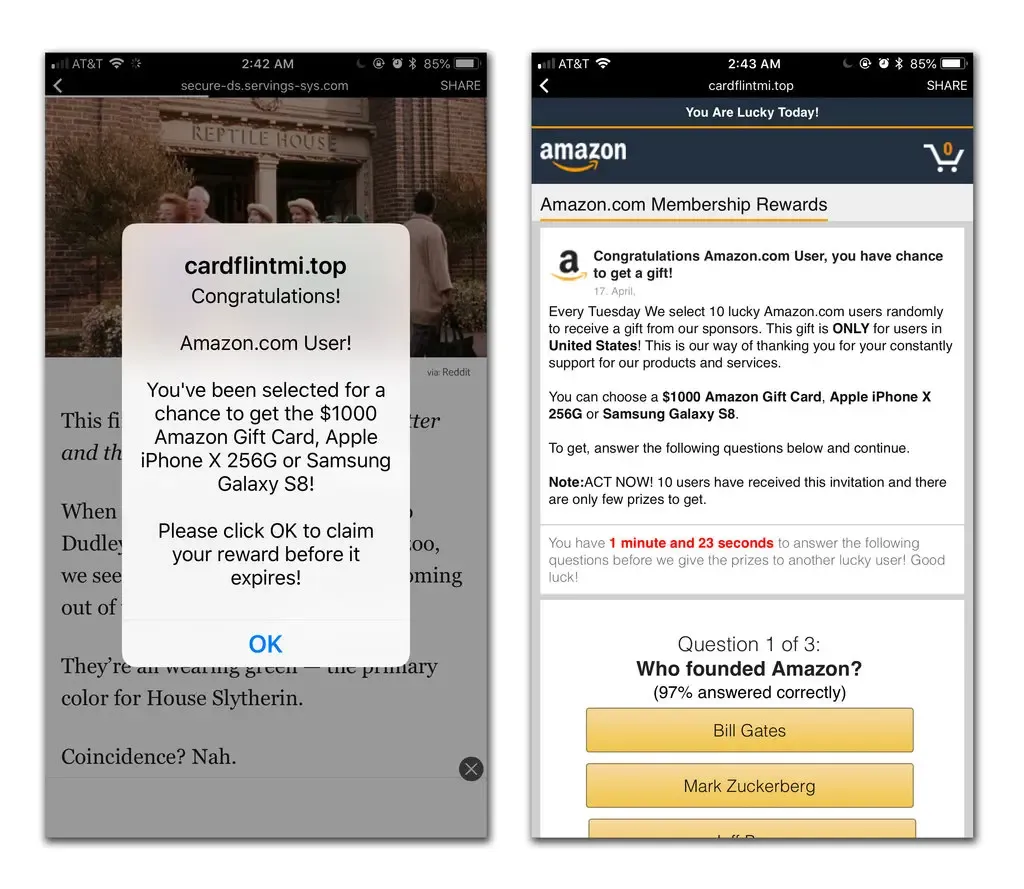
Fake sales and promotions
Malvertising is a type of cyberattack in which perpetrators take advantage of the complex online advertising ecosystem and inject malicious code into legitimate online advertising networks. Multiple redirections between servers occur when a user clicks on an online ad. Attackers exploit this complexity to place malicious content on a publisher’s webpage. Viewing or clicking such a malvertisement (see Figure 4) with a fake sale or promotion can expose users to cyberthreats like malware installation or rerouting to a phishing website.
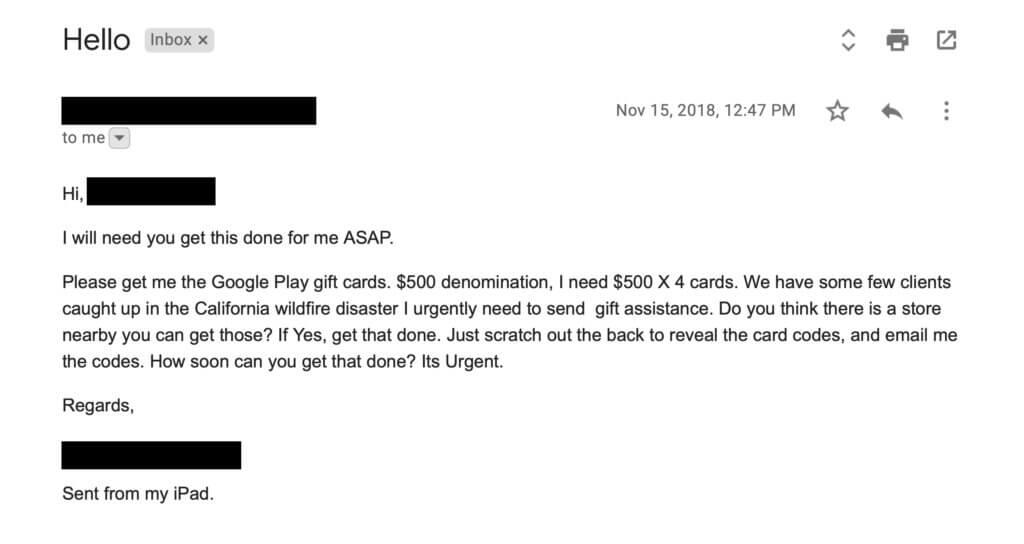
Gift card phishing scams
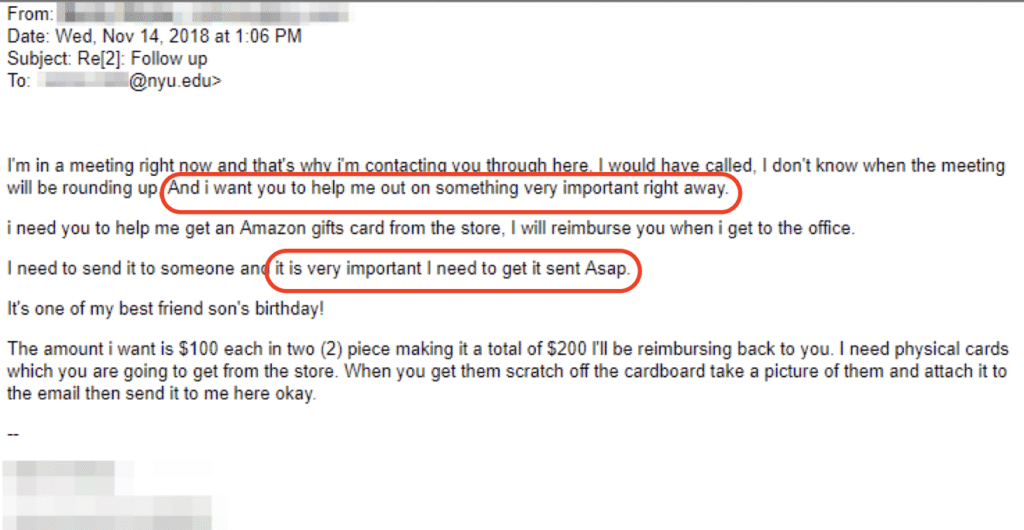
Gift card scams are one of the most sophisticated holiday phishing scams that rely on social engineering tactics. Such scams are designed to impersonate high-level executives within an organization and leverage authority or urgency in the requests to make a lower-level employee purchase a gift card and share its details. Check Figure 5, for instance, where the scammer is purporting as the employee’s colleague.
How to avoid these holiday phishing scams
Let’s now look at some measures individuals can take to avoid falling victim to these holiday phishing scams.
Practice good cybersecurity hygiene
Good cybersecurity hygiene is the first step toward avoiding phishing scams. Never open a link in an email or message unless you are certain it’s authentic. Instead, you can always search for a company’s valid URL in a new browser window — a quick internet search is all it takes to uncover a genuine web address. Similarly, never disclose login credentials, bank account or credit card information via emails. Banks or other businesses don’t ask for such information via email. It is also important not to click on unexpected or suspicious attachments in such emails, as most might contain malware.
Know your buyer/seller
Before purchasing from a business for the first time, do the groundwork. Verify the seller’s legitimacy before going forward — do the basic research, ensure the web address has HTTPS authentication and check reviews. Don’t give away any information until you verify the legitimacy of your buyer or seller.
Be wary of how you pay
Be aware of the pre-paid gift card scams. In such scams, the seller will ask you to pay for the purchase with gift cards. They will ask to send them a gift card, like a Google Play or iTunes card, and its PIN. The scammer will steal your funds and you will never receive the item. Any seller who demands to be paid exclusively with a gift card is likely a scammer. Use a credit card for online shopping and check the statement regularly for suspicious transactions. Contact the credit card company as and when you spot a questionable transaction and dispute the charges.
Deals too good to be true
If a shopping deal seems too good to be true, it probably is; always keep an eye out for such sales. It’s difficult to resist the temptation to check out a rock-bottom price on the new iPhone 14 or another gadget you’ve been eyeing. Scammers know that such deals are an easy way to make people click on malicious links.
How to protect your organization from holiday phishing scams
Holiday phishing scams are here to stay and there is no cookie-cutter approach to prevent them. However, businesses can take the following proactive steps to manage and mitigate such threats.
Cybersecurity as a part of your corporate culture
The cyberthreat landscape is ever-evolving, and as a company’s cyber-risks evolve, so must its culture. At the core of a robust cybersecurity culture is the recognition that people are at the center of it, not technology. Employees are both the weakest and strongest links in a cybersecurity chain. It is thus critical to foster an environment where employees act as the first line of defense. Organizations must encourage their employees to report security incidents or suspicious instances to their security team as soon as they occur or are discovered. Comprehensive security policies and incident response plans must be in place that detail how a business would respond to a cybersecurity incident, including the incident response teams, lines of communication, action plans and so on. This will help minimize the damage and contain the situation efficiently.
Education and training of employees
As discussed above, employees are the first line of defense against cyberthreats. Phishing scams are designed to exploit this human factor through creative and luring attempts, reinforcing the need for continuous employee education and training on cybersecurity. A strong security awareness training program will prepare the workforce for phishing threats through up-to-date educational content, follow-ups and ongoing messaging, testing via simulation and periodical assessments.
Two-factor or multifactor authentications
Gone are the days when “Password123” could pass for securing your data. Passwords have become easy to steal or crack via brute-force attacks. That’s why two-factor or multifactor authentication becomes crucial for organizations to reduce cyber-risks and secure accounts and data effectively. The additional layer of security makes it harder for cybercriminals to access the data and forces them to look elsewhere.
Cybersecurity tools
Leveraging cybersecurity tools to improve your organization’s security posture is a no-brainer in today’s burgeoning threat landscape. An organization can make use of various tools to manage and mitigate phishing threats, like antivirus, antimalware, anti-phishing software and user credential monitoring programs.
Back up data
Phishing attacks can and will strike, and you must have a multilayered strategy to prevent these attacks. Backing up the data is the best ultimate defense on that front since it minimizes the damage in the event of a phishing attack. It is a significant part of an organization’s business continuity strategy since it helps the organization recover swiftly from a cybersecurity incident and continue its operations with minimal or no downtime.
Safeguard your data from holiday phishing scams with the unified BCDR solution
Unified BCDR enables protection for data no matter where it resides: on-prem, on remote endpoints, or within the cloud and SaaS applications. Security integrations, coupled with backup and recovery capabilities, augment the platform to help organizations reduce the frequency and severity of data loss.
Spanning Backup, our cloud-native protection for SaaS applications, offers layered protection through automated phishing defense. Patented AI technology analyzes more than 50 attributes of employee communication to establish profiles of a trusted relationship. It also empowers employees to defend against phishing attempts with visual cues and actionable buttons, while automated feedback and workflow loops make investigation and resolution seamless for IT teams. On the back end, integrated dark web monitoring performs thousands of refined queries daily to proactively alert on accounts or credentials at risk.
Learn more about the industry’s most comprehensive data loss protection solution for SaaS applications like Microsoft 365.